Hi,
i got several wifi connection issues with the previous version 3.5.2. Now, since 3.5.3 no WiFi connection issues. Seems to be stable now.
→ Would give with with this version a try, to get MQTT work. This fails on my site.
My Setup - Private IP CLASS C (IoT on VLAN 5)
Network: 192.268.50.0/24
DHCP Server: 192.168.50.1
DNS Server: 192.168.50.150 (AdGuard Home)
MQTT: 192.168.50.220 ( Broker - mosquitto v2.0.15) on port 1883 (user “nuki” pw sha256 hashed WiFi password (lowercase). )
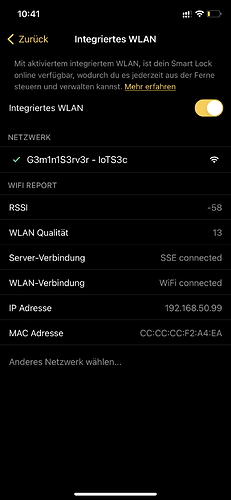
Nuki Client WiFi: SSID IoT on 2.4Ghz Only. RSSI:-58 WiFi-Quality: 13 Nuki Client IP: 192.168.50.99
MQTT Setup
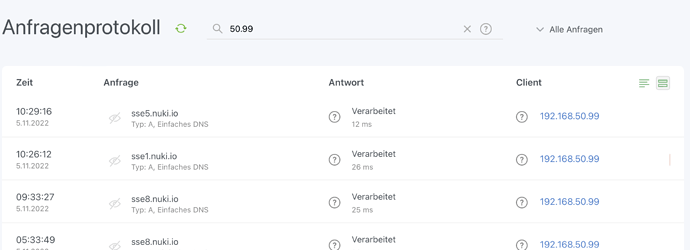
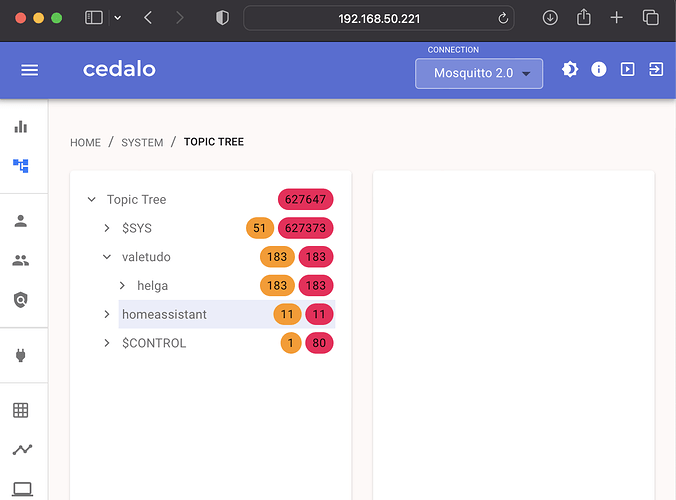
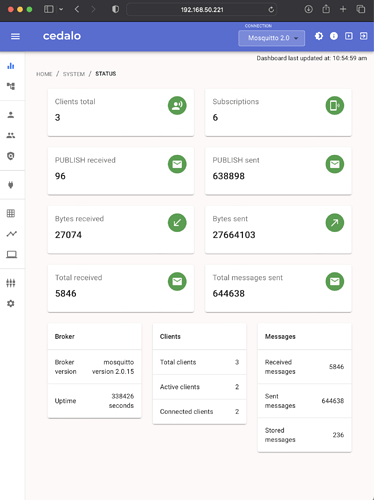
Any DNS request to mqtt and mqtt.local are resolved to the ip address 192.168.50.220. This is also verified with ping on local machines and also with another mqtt devices. So, from network site the Brocker is reachable and is working. Info - Screenshot on bottom.
After Nuki Client is connected to the WiFi it receives the IP address from DHCP and it will also reuest the sseX.nuki.io. In this Example it retrieves the sse5.nuki.io (82.165.250.36). Connection to SSE is now successful and established. I can also see and confirm the DNS request “sse5.nuki.io” on the DNS Server. ![]()
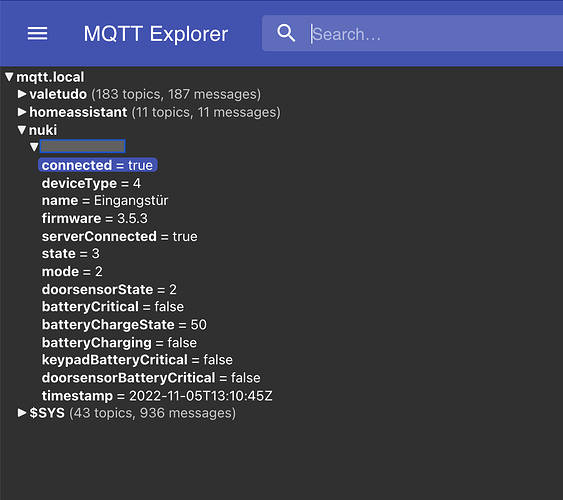
![]() There is no DNS request coming from the Nuki Client to mqtt either to mqtt.local.
There is no DNS request coming from the Nuki Client to mqtt either to mqtt.local.
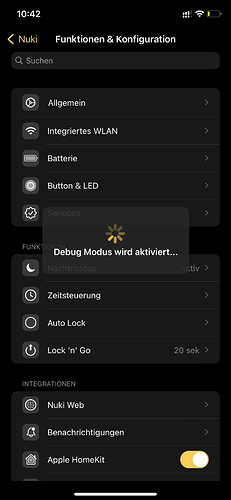
Debug in the iOS Nuki App is enabled! (Tap 7 times with the corresponding information that the debug mode is activated. )
Trace:
After no DNS requests came in the direction of mqtt, I started to analyse what was happening. For me it seems that Nuki is not requesting the mqtt dns. It is using the sse5.nuki.io to try to get a mqtt connection. Please correct me if i’ma wrong. You see in the trace, what the nuki connects with port 443 (https) to nuki server sse5.nuki.io.
![]() -->This connection seems OK for me!
-->This connection seems OK for me!
DstIP: 82.165.250.36, SrcIP: 192.168.50.99, Len: 93, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 443, SrcPort: 52657, Flags: PA
![]() Not OK. This should no be happen. Why is there connection going out to sseX.nuki.io at port 1883?
Not OK. This should no be happen. Why is there connection going out to sseX.nuki.io at port 1883?
DstIP: 87.106.198.152, SrcIP: 192.168.50.99, Len: 42, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 1883, SrcPort: 52658, Flags: PA
Here the full trace!
[DHCP] 2022/11/05 10:29:14,749
DHCP Rx (LAN-1, IOT):
DHCP Client Message (request) from 0.0.0.0: DHCPDISCOVER
Op = 01 | HType = 01 | HLen = 06 | Hops = 00
XId = 55075020 | Secs = 0000 | Flags = 0000
CIAdr = 0.0.0.0 | YIAdr = 0.0.0.0
SIAdr = 0.0.0.0 | GIAdr = 0.0.0.0
CHAdr = cc cc cc f2 a4 ea 00 00 00 00 00 00 00 00 00 00
MsgSize: 1500
Option List 1 3 28 6
=> Tx ARP-Request for 192.168.50.99 on IOT
[DHCP] 2022/11/05 10:29:15,085
DHCP: ARP-Reply for 192.168.50.99
=> Tx DHCPOFFER
[DHCP] 2022/11/05 10:29:15,085
DHCP Tx (LAN-1, IOT):
DHCP Server Message (reply) to 255.255.255.255: DHCPOFFER
Op = 02 | HType = 01 | HLen = 06 | Hops = 00
XId = 55075020 | Secs = 0000 | Flags = 0000
CIAdr = 0.0.0.0 | YIAdr = 192.168.50.99
SIAdr = 0.0.0.0 | GIAdr = 0.0.0.0
CHAdr = cc cc cc f2 a4 ea 00 00 00 00 00 00 00 00 00 00
Server-ID: 192.168.50.1
Netmask: 255.255.255.0
Gateway: 192.168.50.1
DNS-Server: 192.168.50.150
Domain: intern
Broadcast: 192.168.50.255
NBNS-Server: (none)
Leasetime: 14400
T1: 7200
T2: 12600
[DHCP] 2022/11/05 10:29:16,381
DHCP Tx (LAN-1, IOT):
DHCP Server Message (reply) to 255.255.255.255: DHCPOFFER
Op = 02 | HType = 01 | HLen = 06 | Hops = 00
XId = 55075020 | Secs = 0000 | Flags = 0000
CIAdr = 0.0.0.0 | YIAdr = 192.168.50.99
SIAdr = 0.0.0.0 | GIAdr = 0.0.0.0
CHAdr = cc cc cc f2 a4 ea 00 00 00 00 00 00 00 00 00 00
Server-ID: 192.168.50.1
Netmask: 255.255.255.0
Gateway: 192.168.50.1
DNS-Server: 192.168.50.150
Domain: intern
Broadcast: 192.168.50.255
NBNS-Server: (none)
Leasetime: 14400
T1: 7200
T2: 12600
[DHCP] 2022/11/05 10:29:16,471
DHCP Rx (LAN-1, IOT):
DHCP Client Message (request) from 0.0.0.0: DHCPREQUEST
Op = 01 | HType = 01 | HLen = 06 | Hops = 00
XId = 55075020 | Secs = 0000 | Flags = 0000
CIAdr = 0.0.0.0 | YIAdr = 0.0.0.0
SIAdr = 0.0.0.0 | GIAdr = 0.0.0.0
CHAdr = cc cc cc f2 a4 ea 00 00 00 00 00 00 00 00 00 00
MsgSize: 1500
Req.-IP: 192.168.50.99
Server-ID: 192.168.50.1
Option List 1 3 28 6
=> Tx DHCPACK
[DHCP] 2022/11/05 10:29:16,471
DHCP Tx (LAN-1, IOT):
DHCP Server Message (reply) to 255.255.255.255: DHCPACK
Op = 02 | HType = 01 | HLen = 06 | Hops = 00
XId = 55075020 | Secs = 0000 | Flags = 0000
CIAdr = 0.0.0.0 | YIAdr = 192.168.50.99
SIAdr = 0.0.0.0 | GIAdr = 0.0.0.0
CHAdr = cc cc cc f2 a4 ea 00 00 00 00 00 00 00 00 00 00
Server-ID: 192.168.50.1
Netmask: 255.255.255.0
Gateway: 192.168.50.1
DNS-Server: 192.168.50.150
Domain: intern
Broadcast: 192.168.50.255
NBNS-Server: (none)
Leasetime: 14400
T1: 7200
T2: 12600
[IP-Router] 2022/11/05 10:29:19,970
IP-Router Rx (LAN-1, IOT, RtgTag: 5):
DstIP: 82.165.250.36, SrcIP: 192.168.50.99, Len: 44, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 443, SrcPort: 52657, Flags: S
Seq: 2279739, Ack: 0, Win: 11680, Len: 0
Option: Maximum segment size = 1460
Route: WAN Tx (INET_VDFN)
[IP-Router] 2022/11/05 10:29:19,976
IP-Router Rx (LAN-1, IOT, RtgTag: 5):
DstIP: 82.165.250.36, SrcIP: 192.168.50.99, Len: 44, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 443, SrcPort: 52657, Flags: S
Seq: 2279739, Ack: 0, Win: 11680, Len: 0
Option: Maximum segment size = 1460
Route: WAN Tx (INET_VDFN)
[IP-Router] 2022/11/05 10:29:19,985
IP-Router Rx (INET_VDFN, RtgTag: 5):
DstIP: 192.168.50.99, SrcIP: 82.165.250.36, Len: 44, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 52657, SrcPort: 443, Flags: SA
Seq: 2044502082, Ack: 2279740, Win: 29200, Len: 0
Option: Maximum segment size = 1460
Route: LAN-1 Tx (IOT)
[IP-Router] 2022/11/05 10:29:19,990
IP-Router Rx (INET_VDFN, RtgTag: 5):
DstIP: 192.168.50.99, SrcIP: 82.165.250.36, Len: 44, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 52657, SrcPort: 443, Flags: SA
Seq: 2044502082, Ack: 2279740, Win: 29200, Len: 0
Option: Maximum segment size = 1460
Route: LAN-1 Tx (IOT)
[IP-Router] 2022/11/05 10:29:20,487
IP-Router Rx (LAN-1, IOT, RtgTag: 5):
DstIP: 82.165.250.36, SrcIP: 192.168.50.99, Len: 135, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 443, SrcPort: 52657, Flags: PA
Seq: 2279740, Ack: 2044502083, Win: 11680, Len: 95
Route: WAN Tx (INET_VDFN)
[IP-Router] 2022/11/05 10:29:20,487
IP-Router Rx (LAN-1, IOT, RtgTag: 5):
DstIP: 82.165.250.36, SrcIP: 192.168.50.99, Len: 40, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 443, SrcPort: 52657, Flags: A
Seq: 2279835, Ack: 2044502083, Win: 11680, Len: 0
Route: WAN Tx (INET_VDFN)
[IP-Router] 2022/11/05 10:29:20,502
IP-Router Rx (INET_VDFN, RtgTag: 5):
DstIP: 192.168.50.99, SrcIP: 82.165.250.36, Len: 40, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 52657, SrcPort: 443, Flags: A
Seq: 2044502083, Ack: 2279835, Win: 29200, Len: 0
Route: LAN-1 Tx (IOT)
[IP-Router] 2022/11/05 10:29:20,502
IP-Router Rx (INET_VDFN, RtgTag: 5):
DstIP: 192.168.50.99, SrcIP: 82.165.250.36, Len: 1492, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 52657, SrcPort: 443, Flags: A
Seq: 2044502083, Ack: 2279835, Win: 29200, Len: 1452
Route: LAN-1 Tx (IOT)
[IP-Router] 2022/11/05 10:29:20,502
IP-Router Rx (INET_VDFN, RtgTag: 5):
DstIP: 192.168.50.99, SrcIP: 82.165.250.36, Len: 1492, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 52657, SrcPort: 443, Flags: A
Seq: 2044503535, Ack: 2279835, Win: 29200, Len: 1452
Route: LAN-1 Tx (IOT)
[IP-Router] 2022/11/05 10:29:20,502
IP-Router Rx (INET_VDFN, RtgTag: 5):
DstIP: 192.168.50.99, SrcIP: 82.165.250.36, Len: 162, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 52657, SrcPort: 443, Flags: PA
Seq: 2044504987, Ack: 2279835, Win: 29200, Len: 122
Route: LAN-1 Tx (IOT)
[IP-Router] 2022/11/05 10:29:20,579
IP-Router Rx (LAN-1, IOT, RtgTag: 5):
DstIP: 82.165.250.36, SrcIP: 192.168.50.99, Len: 40, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 443, SrcPort: 52657, Flags: A
Seq: 2279835, Ack: 2044504987, Win: 11680, Len: 0
Route: WAN Tx (INET_VDFN)
[IP-Router] 2022/11/05 10:29:20,890
IP-Router Rx (INET_VDFN, RtgTag: 5):
DstIP: 192.168.50.99, SrcIP: 82.165.250.36, Len: 162, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 52657, SrcPort: 443, Flags: PA
Seq: 2044504987, Ack: 2279835, Win: 29200, Len: 122
Route: LAN-1 Tx (IOT)
[IP-Router] 2022/11/05 10:29:20,894
IP-Router Rx (LAN-1, IOT, RtgTag: 5):
DstIP: 82.165.250.36, SrcIP: 192.168.50.99, Len: 382, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 443, SrcPort: 52657, Flags: PA
Seq: 2279835, Ack: 2044505109, Win: 11558, Len: 342
Route: WAN Tx (INET_VDFN)
[IP-Router] 2022/11/05 10:29:20,907
IP-Router Rx (LAN-1, IOT, RtgTag: 5):
DstIP: 82.165.250.36, SrcIP: 192.168.50.99, Len: 40, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 443, SrcPort: 52657, Flags: A
Seq: 2280177, Ack: 2044505109, Win: 11558, Len: 0
Route: WAN Tx (INET_VDFN)
[IP-Router] 2022/11/05 10:29:20,912
IP-Router Rx (INET_VDFN, RtgTag: 5):
DstIP: 192.168.50.99, SrcIP: 82.165.250.36, Len: 115, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 52657, SrcPort: 443, Flags: PA
Seq: 2044505109, Ack: 2280177, Win: 30016, Len: 75
Route: LAN-1 Tx (IOT)
[IP-Router] 2022/11/05 10:29:21,346
IP-Router Rx (LAN-1, IOT, RtgTag: 5):
DstIP: 82.165.250.36, SrcIP: 192.168.50.99, Len: 301, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 443, SrcPort: 52657, Flags: PA
Seq: 2280177, Ack: 2044505184, Win: 11483, Len: 261
Route: WAN Tx (INET_VDFN)
[IP-Router] 2022/11/05 10:29:21,360
IP-Router Rx (INET_VDFN, RtgTag: 5):
DstIP: 192.168.50.99, SrcIP: 82.165.250.36, Len: 221, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 52657, SrcPort: 443, Flags: PA
Seq: 2044505184, Ack: 2280438, Win: 31088, Len: 181
Route: LAN-1 Tx (IOT)
[IP-Router] 2022/11/05 10:29:21,403
IP-Router Rx (LAN-1, IOT, RtgTag: 5):
DstIP: 82.165.250.36, SrcIP: 192.168.50.99, Len: 221, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 443, SrcPort: 52657, Flags: PA
Seq: 2280438, Ack: 2044505365, Win: 11302, Len: 181
Route: WAN Tx (INET_VDFN)
[IP-Router] 2022/11/05 10:29:21,420
IP-Router Rx (INET_VDFN, RtgTag: 5):
DstIP: 192.168.50.99, SrcIP: 82.165.250.36, Len: 157, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 52657, SrcPort: 443, Flags: PA
Seq: 2044505365, Ack: 2280619, Win: 32160, Len: 117
Route: LAN-1 Tx (IOT)
[IP-Router] 2022/11/05 10:29:22,031
IP-Router Rx (INET_VDFN, RtgTag: 5):
DstIP: 192.168.50.99, SrcIP: 82.165.250.36, Len: 157, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 52657, SrcPort: 443, Flags: PA
Seq: 2044505365, Ack: 2280619, Win: 32160, Len: 117
Route: LAN-1 Tx (IOT)
[IP-Router] 2022/11/05 10:29:22,673
IP-Router Rx (LAN-1, IOT, RtgTag: 5):
DstIP: 82.165.250.36, SrcIP: 192.168.50.99, Len: 40, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 443, SrcPort: 52657, Flags: A
Seq: 2280619, Ack: 2044505482, Win: 11185, Len: 0
Route: WAN Tx (INET_VDFN)
[IP-Router] 2022/11/05 10:29:31,750
IP-Router Rx (LAN-1, IOT, RtgTag: 5):
DstIP: 87.106.198.152, SrcIP: 192.168.50.99, Len: 44, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 1883, SrcPort: 52658, Flags: S
Seq: 2300071, Ack: 0, Win: 11680, Len: 0
Option: Maximum segment size = 1460
Route: WAN Tx (INET_VDFN)
[IP-Router] 2022/11/05 10:29:31,765
IP-Router Rx (INET_VDFN, RtgTag: 5):
DstIP: 192.168.50.99, SrcIP: 87.106.198.152, Len: 44, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 52658, SrcPort: 1883, Flags: SA
Seq: 4081880790, Ack: 2300072, Win: 64240, Len: 0
Option: Maximum segment size = 1460
Route: LAN-1 Tx (IOT)
[IP-Router] 2022/11/05 10:29:31,834
IP-Router Rx (LAN-1, IOT, RtgTag: 5):
DstIP: 87.106.198.152, SrcIP: 192.168.50.99, Len: 135, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 1883, SrcPort: 52658, Flags: PA
Seq: 2300072, Ack: 4081880791, Win: 11680, Len: 95
Route: WAN Tx (INET_VDFN)
[IP-Router] 2022/11/05 10:29:31,849
IP-Router Rx (INET_VDFN, RtgTag: 5):
DstIP: 192.168.50.99, SrcIP: 87.106.198.152, Len: 40, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 52658, SrcPort: 1883, Flags: A
Seq: 4081880791, Ack: 2300167, Win: 64145, Len: 0
Route: LAN-1 Tx (IOT)
[IP-Router] 2022/11/05 10:29:31,849
IP-Router Rx (INET_VDFN, RtgTag: 5):
DstIP: 192.168.50.99, SrcIP: 87.106.198.152, Len: 44, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 52658, SrcPort: 1883, Flags: PA
Seq: 4081880791, Ack: 2300167, Win: 64145, Len: 4
Route: LAN-1 Tx (IOT)
[IP-Router] 2022/11/05 10:29:31,858
IP-Router Rx (LAN-1, IOT, RtgTag: 5):
DstIP: 87.106.198.152, SrcIP: 192.168.50.99, Len: 68, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 1883, SrcPort: 52658, Flags: PA
Seq: 2300167, Ack: 4081880795, Win: 11676, Len: 28
Route: WAN Tx (INET_VDFN)
[IP-Router] 2022/11/05 10:29:31,872
IP-Router Rx (INET_VDFN, RtgTag: 5):
DstIP: 192.168.50.99, SrcIP: 87.106.198.152, Len: 40, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 52658, SrcPort: 1883, Flags: A
Seq: 4081880795, Ack: 2300195, Win: 64117, Len: 0
Route: LAN-1 Tx (IOT)
[IP-Router] 2022/11/05 10:29:31,929
IP-Router Rx (LAN-1, IOT, RtgTag: 5):
DstIP: 87.106.198.152, SrcIP: 192.168.50.99, Len: 654, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 1883, SrcPort: 52658, Flags: PA
Seq: 2300195, Ack: 4081880795, Win: 11676, Len: 614
Route: WAN Tx (INET_VDFN)
[IP-Router] 2022/11/05 10:29:31,944
IP-Router Rx (INET_VDFN, RtgTag: 5):
DstIP: 192.168.50.99, SrcIP: 87.106.198.152, Len: 40, DSCP: CS0/BE (0x00), ECT: 0, CE: 0
Prot.: TCP (6), DstPort: 52658, SrcPort: 1883, Flags: A
Seq: 4081880795, Ack: 2300809, Win: 63856, Len: 0
Route: LAN-1 Tx (IOT)
DNS Requests 10:29!
Wifi Settings:
Debug Enabled:
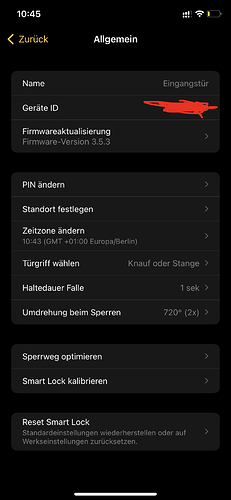
Firmware:
MQTT (Management View):